Information Security Management System Software
In an era of rapid and relentless digital transformation of all spheres, the availability of information dominates every business organization.
• No card required
In an era of rapid and relentless digital transformation of all spheres, the availability of information dominates every business organization.
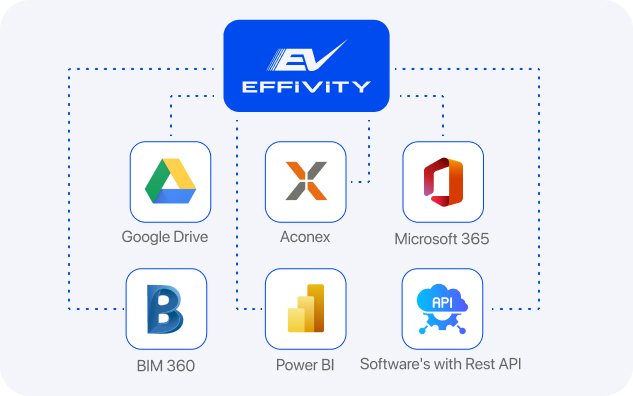
Our unwavering commitment to flexibility and scalability guarantees smooth integration with existing frameworks while laying the foundation for future expansion and growth.
Try Now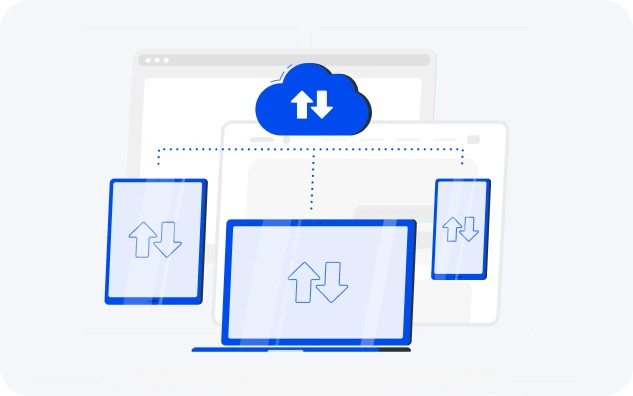
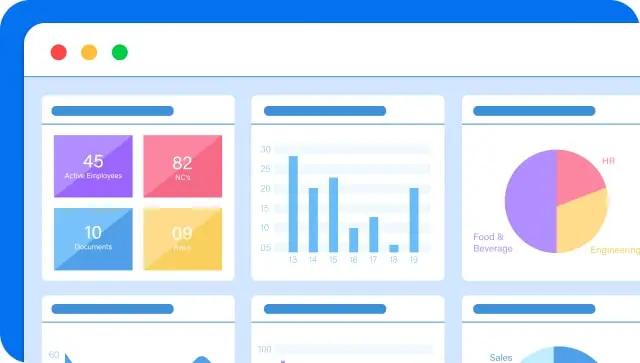
Effivity's cloud-based solutions transform the complex task of compliance management into a streamlined process.
Our Software consolidates all compliance metrics and sensitive data into a centralized repository to enhance internal access while fortifying data security measures.
In the current state of increased cyber threats and data vulnerabilities, Effivity offers a well-rounded, comprehensive solution. Our ISMS software forms a comprehensive line of defense against all digital threats, enabling your organization to safeguard essential data and information and enhance compliance with ISO 27001:2022 standards.
• No card required
An Information Security Management System is a comprehensive framework comprising policies, procedures, and technical and physical control for information security. It is designed to manage and safeguard the sensitive information owned by an organization. An ISMS software simplifies and streamlines the ISMS processes to improve your organization's resilience against cyber threats.
Effivity's ISMS Software blends adaptability, scalability, and precision to help you seamlessly meet ISO 27001:2022 compliance requirements and industry benchmarks and refine your implementation of proactive information security strategies.
In the realm of information security, organizations face several rapidly escalating threats, risks, and challenges. To address these, implementing a robust ISMS is vital. However, implementing an ISMS may not always be straightforward, and some challenges may arise, these include-
✓ Understanding Regulatory Requirements
✓ Training and Awareness
✓ Monitoring and Improvement
✓ Resource Allocation
Effivity's Information Security Management Software is designed to address these potential hurdles depending on your organization's specific requirements.
By focusing on enhanced processes and compliance, our Software ensures that your organization can easily align with key regulations and standards. It is a centralized hub that stores all relevant information and documentation, providing a single-point reference and saving you from extensive paperwork.
With a user-friendly design, Effivity's ISMS Software is easy to navigate with its no-code interface, making the training phase of your ISMS implementations shorter and more efficient. Employees can quickly adapt to changes and reduce their dependence on IT support. As a cloud-based solution, Effivity ensures that you do not need to allocate excessive resources to set up or maintain an ISMS. With quick set-up times and easy integration into existing systems, you can get your ISMS up and running quickly.
Monitoring and improving your ISMS process is simplified with Effivity's Software. With meticulous tracking, automated tasks, and precision, the platform reduces human errors, making audits, monitoring, and improvement more straightforward and accurate.
Effivity's ISMS software is designed with flexibility at its core. We offer modular flexibility, meaning the platform can be tailored to specific organizational needs. You can select the elements your organization needs and then continue customizing the platform as the business landscape evolves.
At Effivity, we understand that questions or hiccups may arise at any time when implementing a new ISMS. To ensure a smooth journey with ISMS, we provide round-the-clock customer support to address every issue promptly, reduce downtime, and ensure smooth operations. Effivity offers 24/7 customer support.
As your organization pivots towards online models and digital operations, protecting your digital infrastructure goes without question. ISMS software ensures that every step in your digital journey is secure against cyber threats and information leaks. Effivity's ISMS Software acts as a shield during your organization's transition.
Meeting regulatory standards such as ISO 27001:2022 increases the trust that clients and stakeholders have in your organization. Effivity's ISMS Software ensures that your organization stays updated on information security regulations and reduces non-compliance risks. Designed with ISO standards in mind, the Software aligns with ISO requirements to fast-track your journey to compliance and certification.
Our ISMS software helps you detect and counteract risks and threats ensuring business continuity and reducing the economic implications of breaches. The Effivity ISMS Software allows your organization to identify potential information security threats and manage risks.
Every piece of information and data is a valuable organizational asset. Assets must be protected vigilantly to ensure unwavering trust in the organization's commitment to integrity. Effivity's Software helps you establish an effective ISMS to create a comprehensive asset protection strategy.
While security is the guiding principle of ISMS software, it also enhances operational flow. It automates processes related to Information Security Management so that resources can be allocated toward core value-driven tasks.
Security breaches can jeopardize an organization's reputation in this digitally interconnected era. Using ISMS software creates a resilient wall against digital threats, safeguarding information and boosting reputation to give your organization a competitive edge.
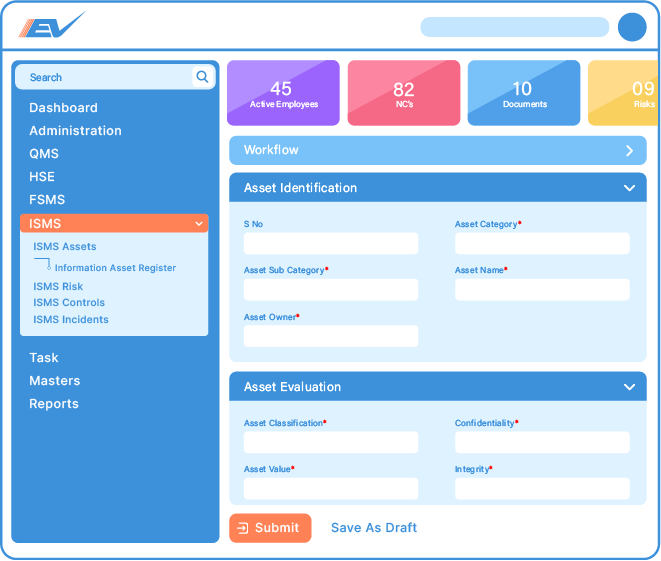
Effivity’s ISMS software is intricately designed with a keen focus on flexibility and customization. With modules that align with the new ISO 27001:2022 requirements, it helps you implement and maintain ISMS effectively in your organization.
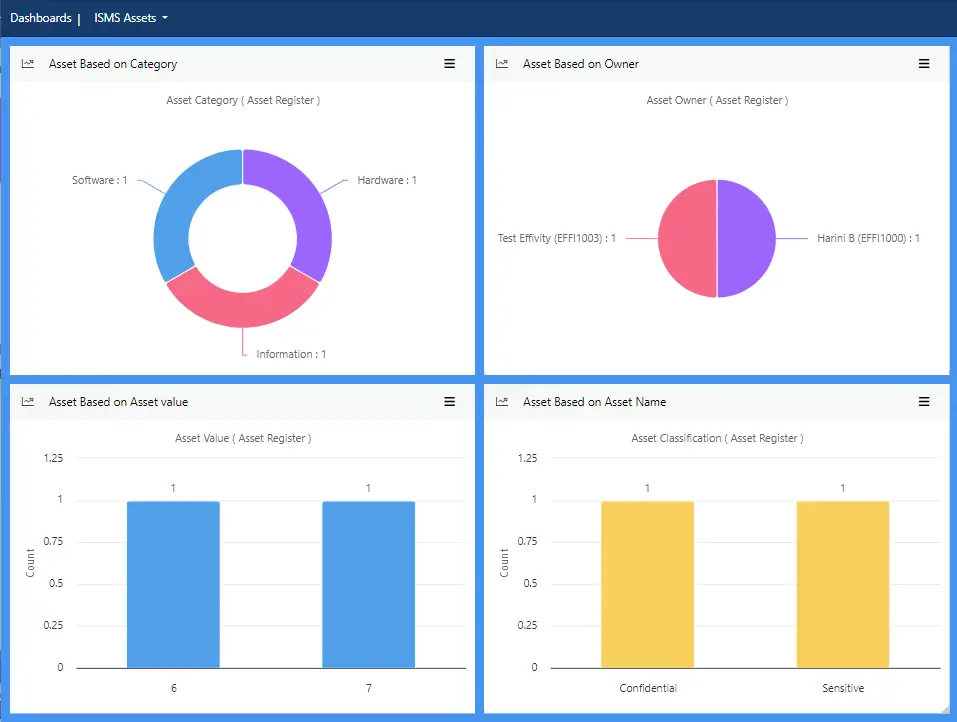
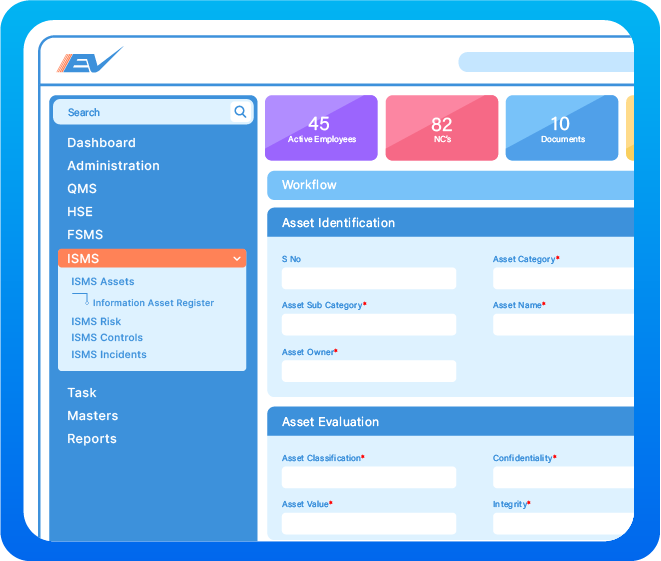
Create a comprehensive overview of your organization’s security assets and determine potential threats and risks with the ISMS Asset Register.
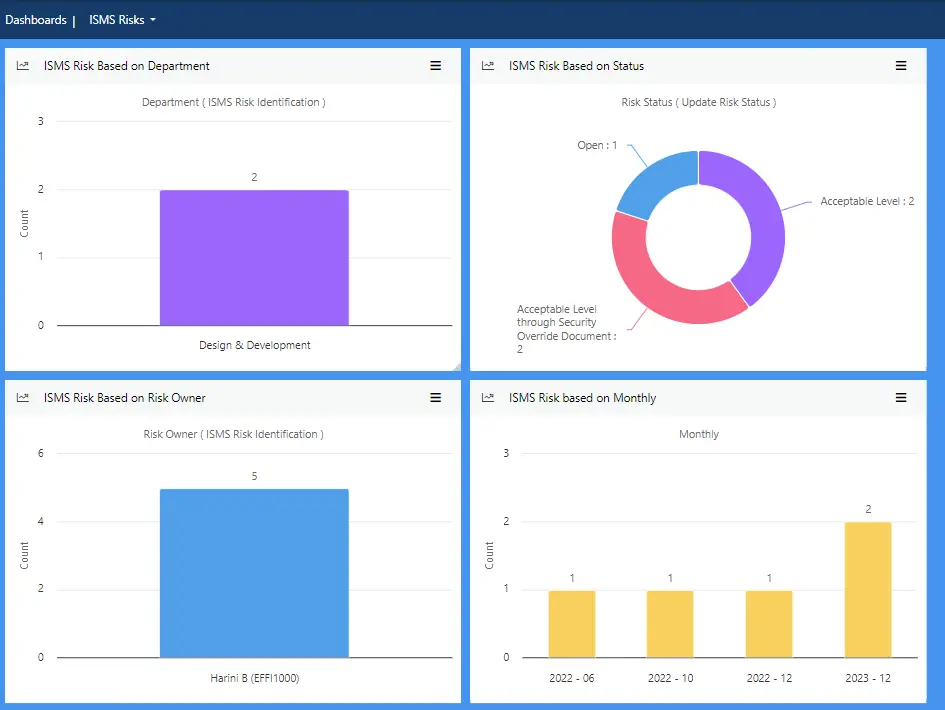
This module leads your organization towards adept risk management with an ISMS Risk Register. You can also create risk treatment plans, conduct risk reassessments, and generate SOAs for residual risks.
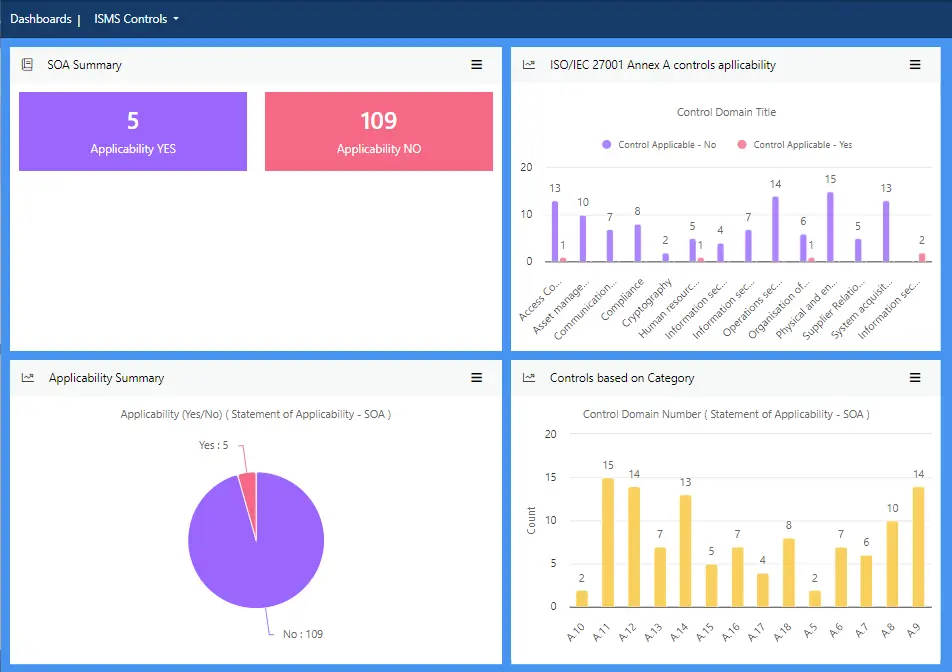
With 114 information security controls, this module lets you choose the appropriate external controls, justify your choice, and automatically generate a Statement of Applicability (SOA).
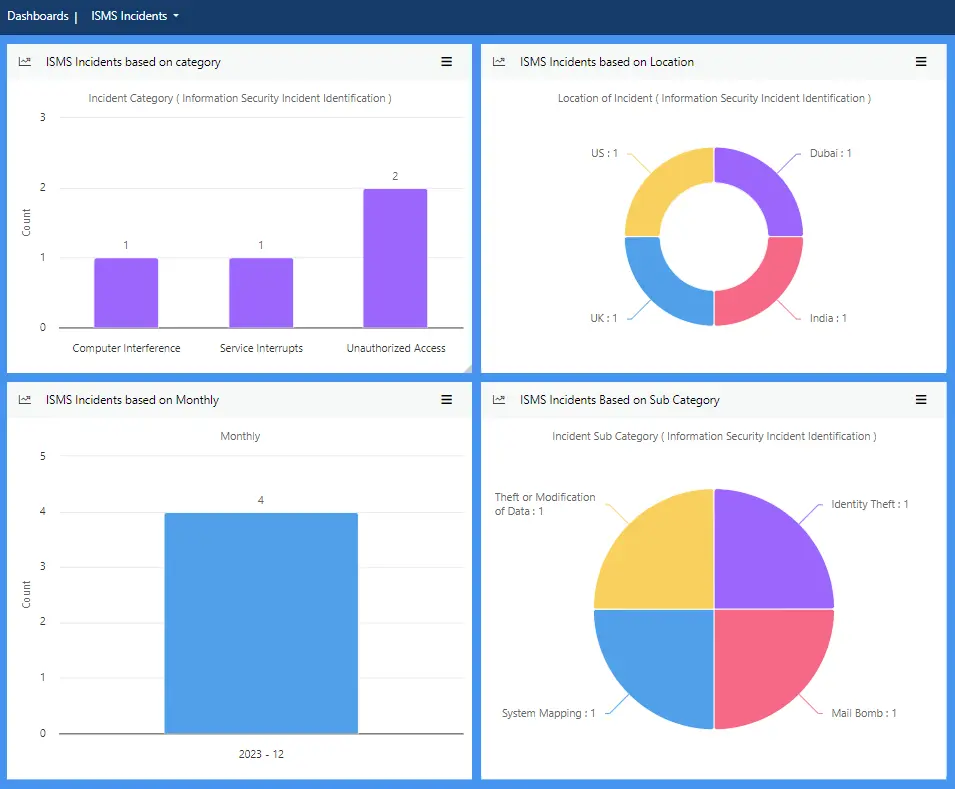
Create a comprehensive record of information security incidents including breaches, leaks and threats. Improving monitoring and risk management with this module.
But there are wider benefits associated with ISMS software that have an impact right across your organisation.These include:
Implementing an ISMS is an intricate process, which means a good place to begin is defining the scope of your ISMS and its objectives. Use Effivity's modules to understand your organization's internal and external risks and opportunities. Define the types of information you are trying to protect and what kind of threats you seek protection against. Next, create SMART objectives based on your policies and ISO 27001 standards.
Implementing an ISMS is an intricate process, which means a good place to begin is defining the scope of your ISMS and its objectives. Use Effivity's modules to understand your organization's internal and external risks and opportunities. Define the types of information you are trying to protect and what kind of threats you seek protection against. Next, create SMART objectives based on your policies and ISO 27001 standards.
The next step is to conduct a thorough risk assessment to identify, analyze, and prioritize various security risks. This can be done with the ISMS software by Effvity, which streamlines this effort and provides a comprehensive picture of vulnerabilities to help you set priorities.
After assessing risks, the next step is establishing strategies and setting controls to counteract threats and vulnerabilities. Effivity's Software assists you in developing appropriate strategies and implementing them across your organization effectively.
Ensuring your employees are acquainted with ISMS protocols is critical for effective implementation. Use Effivity's modules to enhance employee competence and train them on security protocols and procedures.
Continuous monitoring of ISMS strategies and their effectiveness ensures that your organization's information security is always protected. Effivity's cloud-based platform brings all data, documentation, and procedures to one place to simplify and improve the accuracy of your monitoring and review processes.
Your ISMS must evolve with the constantly changing digital landscape. This means that continually identifying areas for improvement is vital to keep your system relevant and functional. Effivity's adaptable platform ensures you can easily modify and customize your ISMS based on evolving organizational needs, regulatory requirements, and industry standards.